Q-Day Part II: Infrastructure Exposure in a Post-Shor Scenario
If Shor’s algorithm can be executed at scale, RSA and ECC-based systems are vulnerable. But migrating cryptographic systems cannot happen overnight. In this article GQI qualifies the risk to real-world systems in the event of a Shor algorithm demonstration on RSA-2048.
Part I of this series examined how the “Pinnacle Architecture” analysis (arXiv:2602.11457) compresses the physical qubit requirement for factoring RSA keys to approximately 100,000 qubits, an order of magnitude reduction from Craig Gidney’s 2025 benchmarks. While significant engineering trade-offs remain, the direction of travel suggests the hardware threshold for a cryptographically relevant quantum computer (CRQC) is descending.
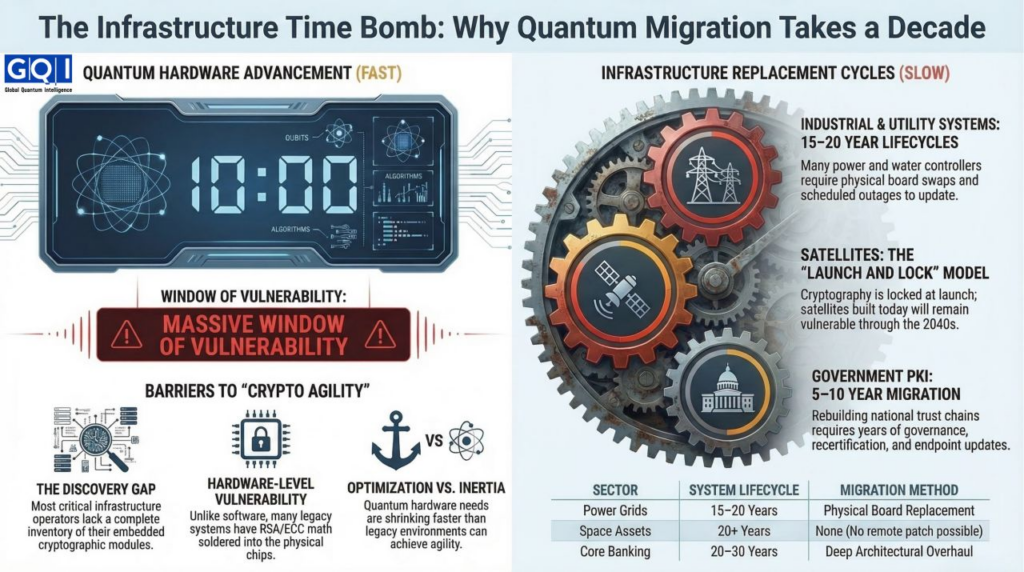
This creates a structural tension. Even if a CRQC remains years away, the systems that could be compromised are embedded in infrastructure with replacement cycles measured in years, possibly up to a decade.
The Installed Base Problem
Unlike software vulnerabilities that can be patched remotely, the cryptographic foundations of many legacy environments are fixed at the hardware level. Three sectors illustrate the scope of the exposure.
Industrial Control Systems and Critical Infrastructure
Power grids, pipeline networks, and water treatment facilities operate on industrial control systems and supervisory control and data acquisition platforms with lifecycles of 15 to 20 years. Many of these systems use classical math based encryption, including RSA, for three distinct purposes: authenticated firmware updates, secure remote access, and device to control center communication.
The migration challenge is not cryptographic but physical. A substation controller manufactured in 2015 may contain a hardware security module soldered to the board. Updating its cryptographic capabilities requires board replacement, which in turn requires scheduled outages and requalification under grid reliability standards. The North American Electric Reliability Corporation Critical Infrastructure Protection standards require testing before hardware changes in bulk power systems. For a typical utility, rotating through every field device for a hardware swap could require up to 10 years of continuous work, assuming no supply chain delays.
Satellite and Space Based Infrastructure
Satellite telemetry, command links, and in orbit firmware updates rely on asymmetric cryptography established at launch. Once a satellite is deployed, its cryptographic capabilities are locked. The average commercial satellite has a design life of 15 years. Government satellites often operate for 20 years or more.
The vulnerability is compounded by the launch and lock model. A satellite built today using RSA for command authentication will remain in orbit through the 2030s and into the 2040s. If a CRQC becomes operational during that window, satellites launched in the preceding years could become vulnerable. There is no patch mechanism for hardware already in orbit. The only mitigation is cryptographic agility designed at the outset, a requirement not yet universal in satellite procurements.
Government Public Key Infrastructure and Code Signing
National digital identity systems, e passport signing keys, and government software update mechanisms are built on trust chains terminating in RSA signed root certificates. Rebuilding these trust anchors is not a technical exercise alone but a governance challenge spanning multiple administrations.
The U.S. federal government operates hundreds of certification authorities across civilian, defense, and intelligence agencies. Migrating the entire federal PKI to post quantum cryptography requires generating new root and intermediate keys, recertifying endpoints, and maintaining parallel trust stores during transition. Federal planners estimate a full migration could require up to five years from final standard adoption to completion.
The Discovery Gap
Before migration can begin, organizations must locate every instance of RSA and ECC in their environments. This is not a trivial exercise.
Cryptographic discovery tools remain immature. Many organizations do not maintain complete inventories of embedded systems, industrial controllers, or legacy application dependencies. A 2025 survey by the Global Cyber Security Capacity Centre found that a majority of critical infrastructure operators could not produce a complete inventory of cryptographic modules in their operational technology environments.
The discovery problem extends into supply chains. A defense contractor may rely on a subcontractor’s component that contains an RSA signed bootloader. The prime contractor may not know the component exists. The harvest now decrypt later risk therefore extends beyond systems an organization controls directly to every supplier in its ecosystem.
Crypto Agility: Concept Versus Capability
Crypto agility, the ability to replace cryptographic algorithms without disrupting operations, is frequently cited as the solution to quantum risk. In practice, true agility remains rare.
Modern cloud native applications designed with cryptographic abstraction layers can achieve algorithm flexibility. But many systems that secure physical infrastructure, pipelines, power plants, satellites, were not designed for abstraction. Their cryptography is often implemented in firmware or embedded in application specific integrated circuits.
For these environments, crypto agility is not a software update but a hardware replacement cycle measured in years.
The Financial Sector Context
Banks present a more complex picture. Core banking systems, mainframes, settlement databases, and SWIFT interfaces often run on codebases decades old. While many Tier 1 institutions have published quantum safe roadmaps and conducted trials, the gap between pilot projects and production deployment across the entire enterprise remains substantial. Retail banking interfaces may achieve agility faster than wholesale payment settlement systems, where transaction finality and regulatory compliance impose additional verification requirements. The sector’s exposure is real, but migration timelines will vary significantly based on system criticality and architectural complexity.
Strategic Observation
The compression of Shor’s resource requirements documented in Part I narrows the window between theoretical capability and engineering reality. But the installed base of systems relying on classical math based encryption operates on a fundamentally different clock, one measured in physical replacement cycles and regulatory requalification.
Migration roadmaps that assume linear progression from standardization to implementation do not fully account for this asymmetry. The systems most exposed to retrospective decryption, industrial controls, space assets, and long lived government archives, are precisely those that cannot be patched overnight.
The relevant question for sovereign risk modeling is no longer solely when will a CRQC exist, but how long will it take to replace every vulnerable system in the critical national infrastructure inventory. For many sectors, that answer remains measured in years, possibly up to a decade.
March 14, 2026